[2 … 3] Conference – ITSecX “Faking at Level 1 – How Digital Twins Save Your PLCs”
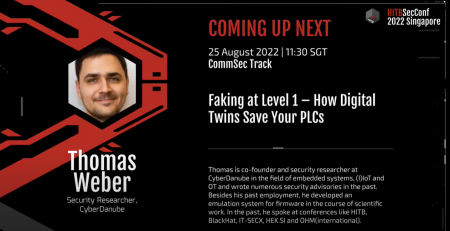
2 out of 3 confirmed conference talks for 2022 – this time at ITSecX. On the 7th of October the well known cyber security conference in Austria took place – IT-Security Community Exchange (IT-SECX) at the St. Pölten University of Applied Sciences !
This years main topic was themed “Cyber Defense” with the keynote “The Law, Policy and Diplomacy of Critical Infrastructure Protection”. Since the topics “Critical Infrastructure Protection” go hand in hand with OT and furthermore with the use of digital twins in particular – we are able to help to outsource emulations in critical environments in order to test in-depth security and facilitate the way with firmware for pentesters. Therefore CyberDanube was in with another talk by Thomas Weber.
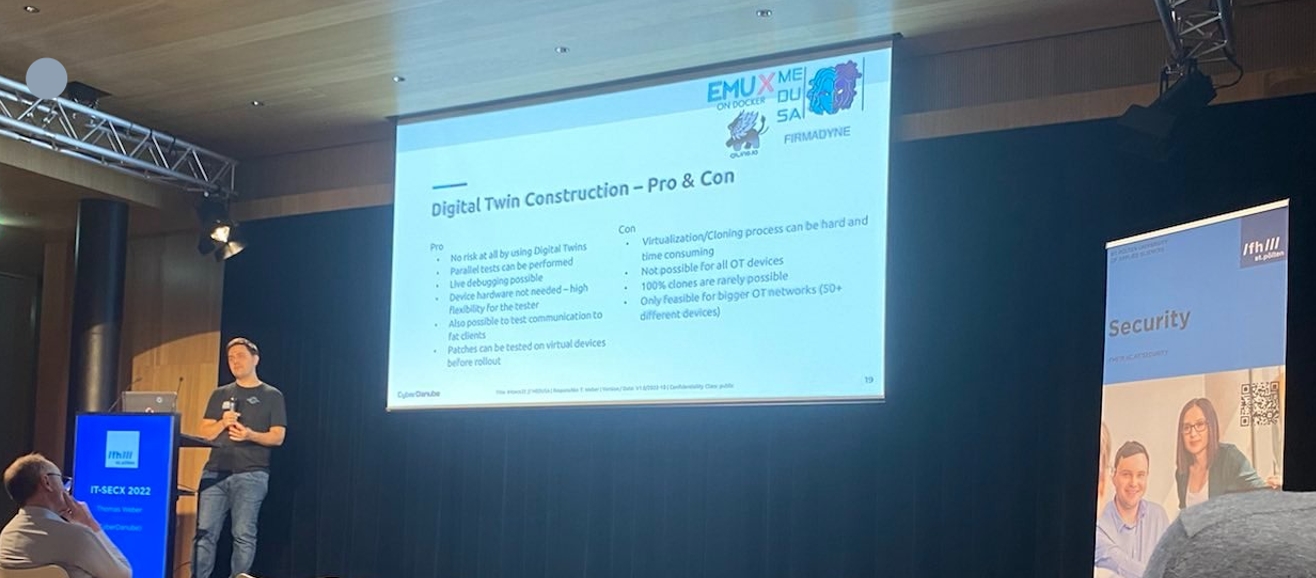
Our talk titled “Faking at Level 1 – How Digital Twins Save Your PLCs ” was therefore the perfect match to expand the requirements and possibilities regarding embedded security in critical infrastructure.
For those who couldn’t made it there, follow the link an watch the talk on YouTube.
Talk Content
For more information, download the lectures and/or watch the recording on YouTube.