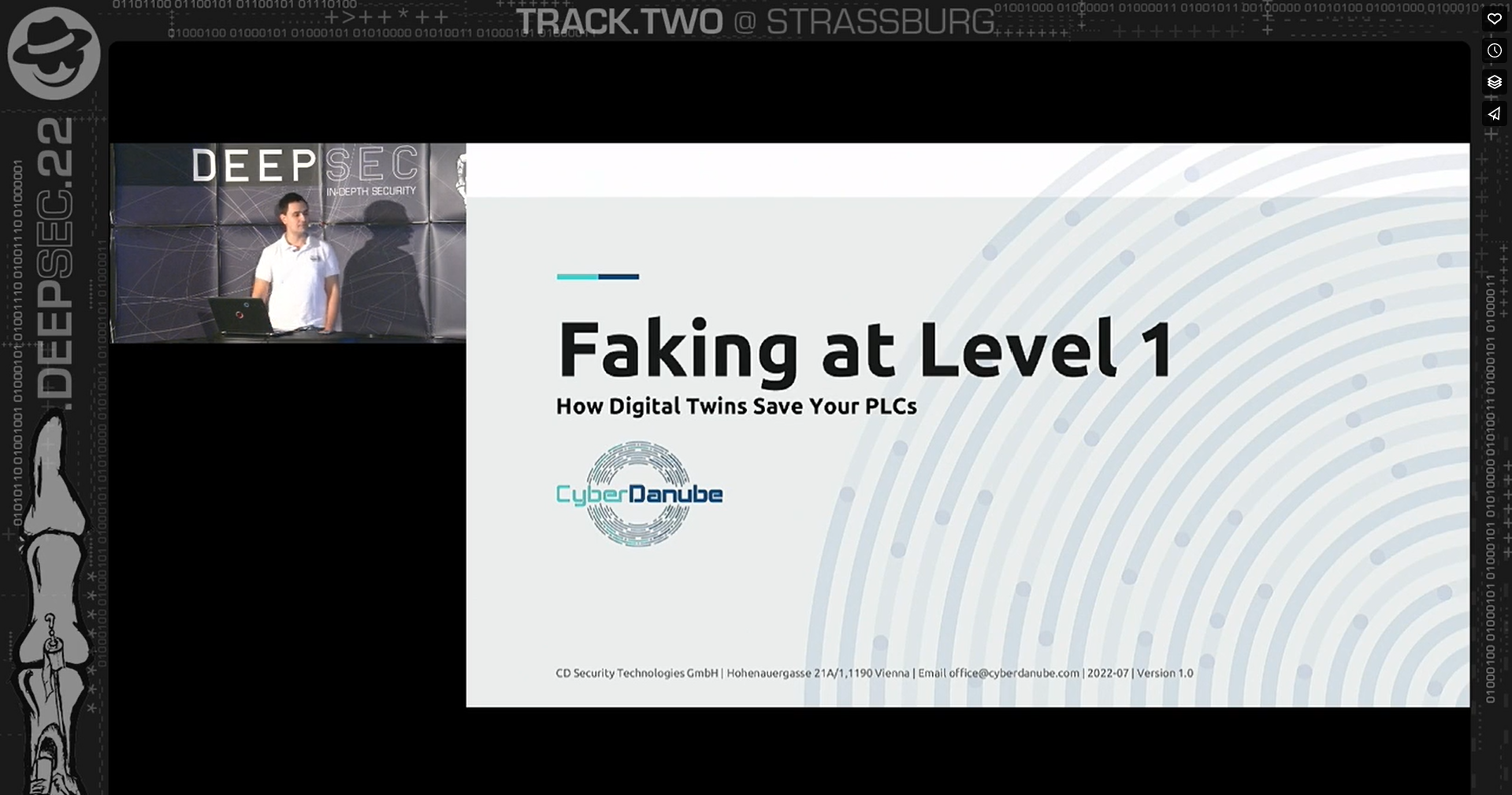
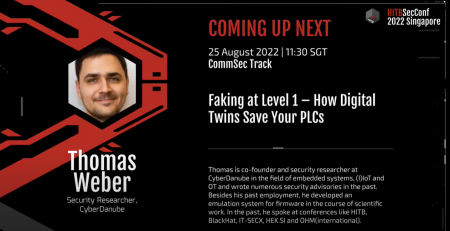
[3 … 3] Conference – DeepSec 2022 “Faking at Level 1 – How Digital Twins Save Your PLCs”
3 out of 3 confirmed conference talks in 2022!
Looking back on a successfull conference marathon so far. DeepSec was a blast!
DeepSec is a very specialized and a technically deep-dive infosec event. CyberDanube had some really good conversations and some deep OT and IoT/IIoT discussions regarding our product MEDUSA. We got the chance to meet exciting contacts and made some future opportunities.
On top we had the pleasure to talk about our main topics of “digital twins out of firmware to support e.g. security assessments”, especially in critical environments on PLCs. Now, we are looking back to a successfull 2022 and further conferences like this one in 2023.
Read a short interview in advanced:
DeepSec 2022 Talk: Faking at Level 1 – How Digital Twins Save Your PLCs – Thomas Weber
For those who have not enough yet … spoiler alarm – all talks are summarized in a book! As soon as it’s available, we’ll share an update on our social media channels.
Talk Content
For all those who would like to see the corresponding slides of the talk(s) follow the link: